I agree, being met with suspicion on my first post about something concerning when being prevented from providing the most bit-exact method of proof by the forum software’s anti-spam is also an unpleasant experience on my end.
Upon perusal, I found no procedure for private reporting of security issues. I followed the reporting template, with cat /etc/release output and all relevant points from “How to get better results when posting about problems” included. I see no other relevant pinned threads, and you have provided no information what information is missing.
I will attempt to repost the screenshots here, in the hope the anti-spam measures have deemed me worthy:
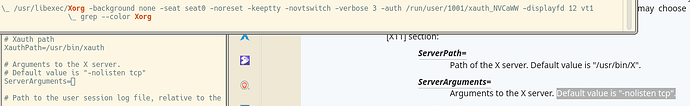
Unmodified SDDM configuration:
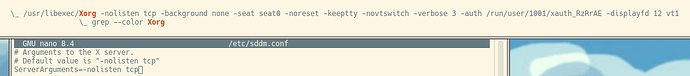
After adding the flag:
The issue is obvious from the images, and no amount of typing increases the verifiability of the claims, but for those who only parse ASCII, sddm.conf looked like this
# Arguments to the X server.
# Default value is "-nolisten tcp"
ServerArguments=
There was no flag, and the x server was not running with -nolisten tcp by default as the comment claimed.
man xserver
-nolisten trans‐type
disables a transport type. For example, TCP/IP connec‐
tions can be disabled with -nolisten tcp. This option may
be issued multiple times to disable listening to different
transport types. Supported transport types are platform
dependent, but commonly include:
tcp TCP over IPv4 or IPv6
inet TCP over IPv4 only
inet6 TCP over IPv6 only
unix UNIX Domain Sockets
local Platform preferred local connection method
Therefore, from the information provided, the default SDDM configuration for OpenMandriva Rock opens up the X server to remote connections, which would seem to be a significant security issue that should be directed to the community out of a desire for social good, rather than just fixing it for myself.
I’ve confirmed that other distros run with this flag enabled by default, so unwarrented defensiveness that avoids the issue in preference of unrelated accusations warrants suspicion in itself. As the pinned thread states, you’re not paid to respond, but please keep the thread on topic from now on. If there is more relevant information that either of us can provide to resolve the issue, that would be a great direction.
Thank you.